Two-factor authentication is becoming a security standard for large organizations. Many of you are already accustomed to using Duo to authenticate to any University services.
In order to help ensure a more secure network, two-factor authentication is now required for logging into OSU Engineering servers for terminal or SFTP access.
This can cause problems for those not using an interactive terminal session, as there is an additional prompt that requires a response and the connection fails silently.
We can bypass the need for DUO authentication by setting up SSH Keys for our applications that use SFTP
This guide only applies to Windows 11 and newer versions of Windows 10 (build 1809+). For older versions of Windows, please follow the instructions under "Using PuTTY" or check Microsoft's website on how to enable OpenSSH Client for Windows.
ssh-keygen -t rsaenter. Then hit enter two more times to skip creating a passcode.%UserProfile%\.ssh\id_rsa.pub with this location, such as C:\Users\your_username\.ssh\my_key.pub.1 and press enter. This will send a request to your Duo Mobile app which you will need to acceptssh your_username@access.engr.oregonstate.edu -i %UserProfile%\.ssh\id_rsa at the terminal command line prompt. If you saved the key to a location other than the default, replace %UserProfile%\.ssh\id_rsa with this location, such as C:\Users\your_username\.ssh\my_key. If successful, you will connect without having to enter a password or do two-factor authentication!First, download FileZilla (available here)
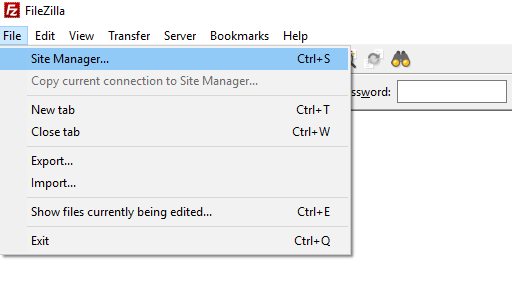
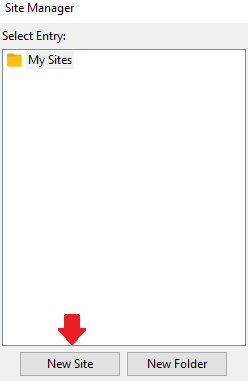
Open FileZilla and go to File->Site Manager
SFTP for the Protocol and enter the Host as access.engr.oregonstate.edu.Key file, enter your username for User, and then browse to the location of your `id_rsa' file. You may have to change the dropdown to "All files (*.*)" in the File Explorer window to show your "id_rsa" file./Applications/Utilities/Terminal.app) 
ssh-keygen -t rsaenter. Then hit enter two more times to skip creating a passcodessh-copy-id -i ~/.ssh/id_rsa.pub your_ONID@access.engr.oregonstate.edu. This will publish your public key to the engineering servers.1 to send a push to your Mobile Duo appssh your_ONID@access.engr.oregonstate.edu at the terminal command line prompt. If successful, you will connect without having to enter a password or do two-factor authentication!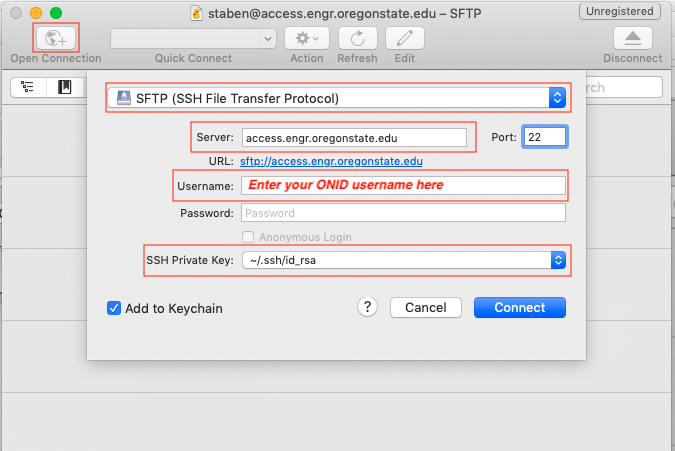
Dreamweaver does not like the the SSH Key format generated by the latest version of OpenSSH and the ssh-keygen untility. If you are running a recent version of macOS, including Mojave. You will need to "downgrade" your id_rsa file using the folloing command in the Terminal app:
ssh-keygen -p -m PEM -f ~/.ssh/id_rsa
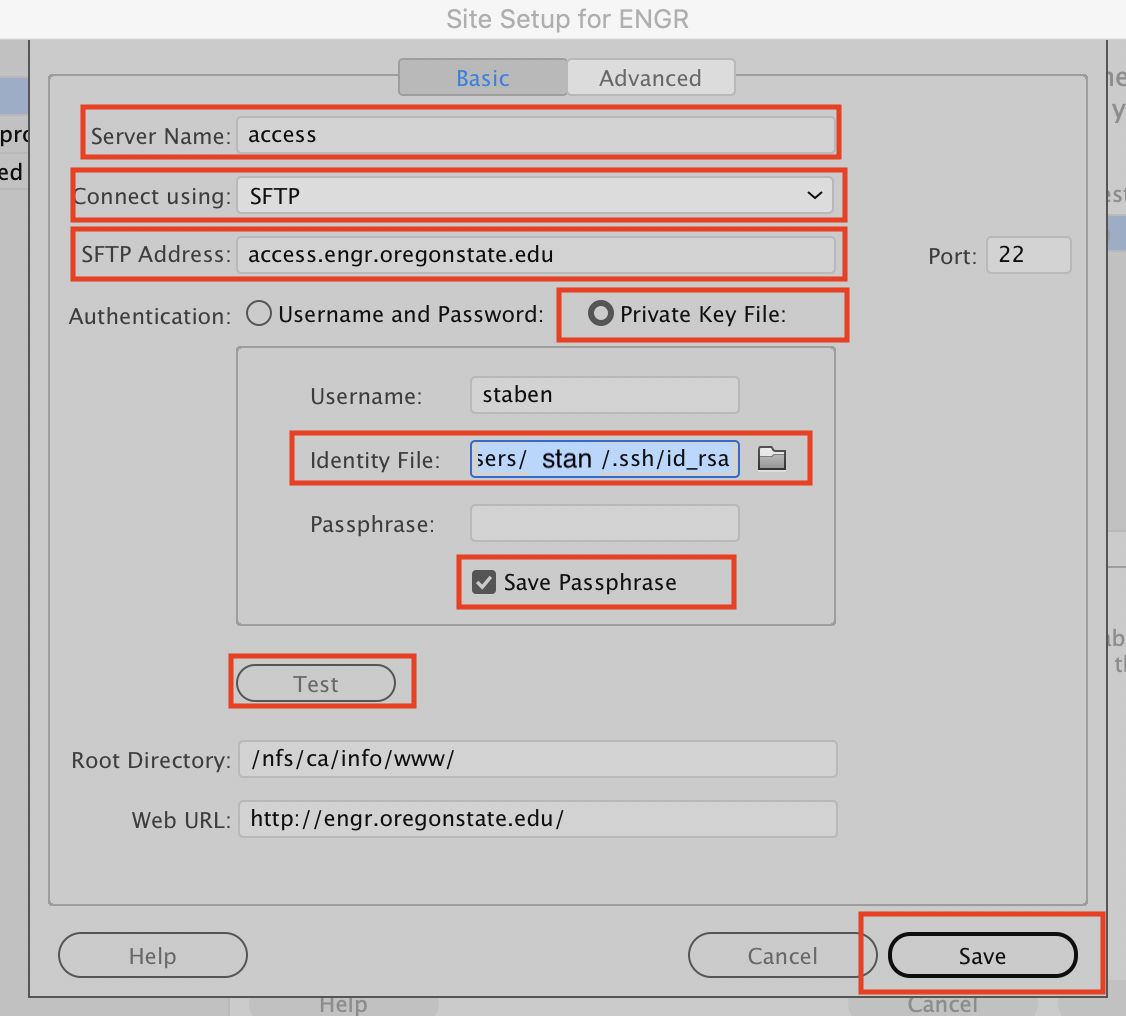
Now continue to set up Dreamweaver:
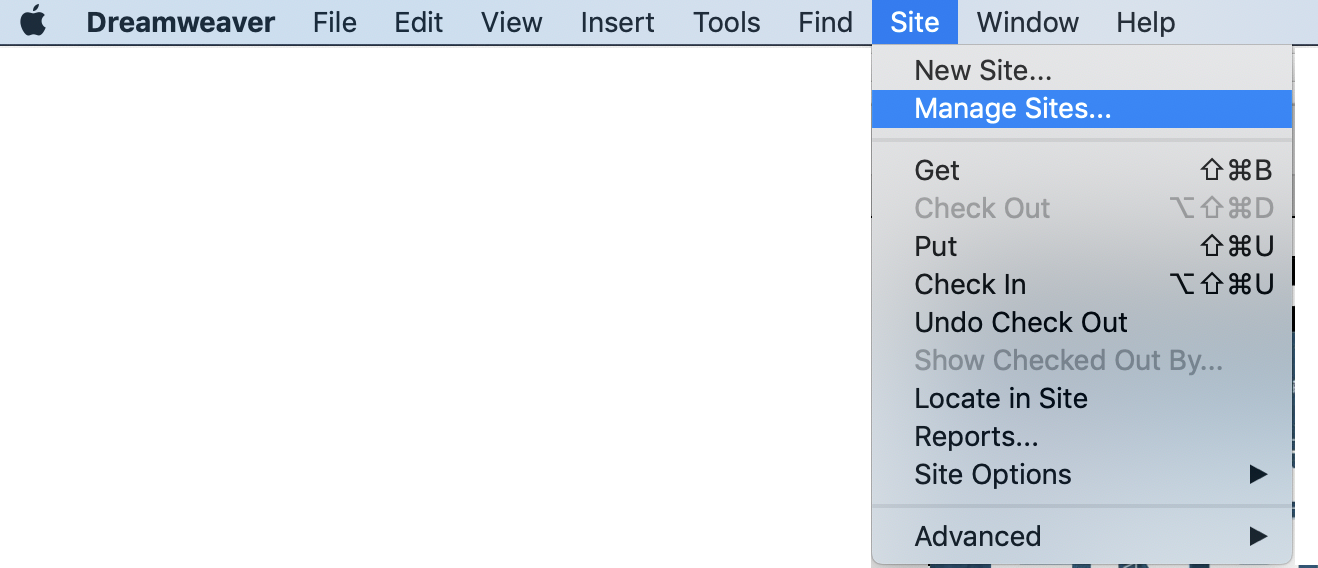
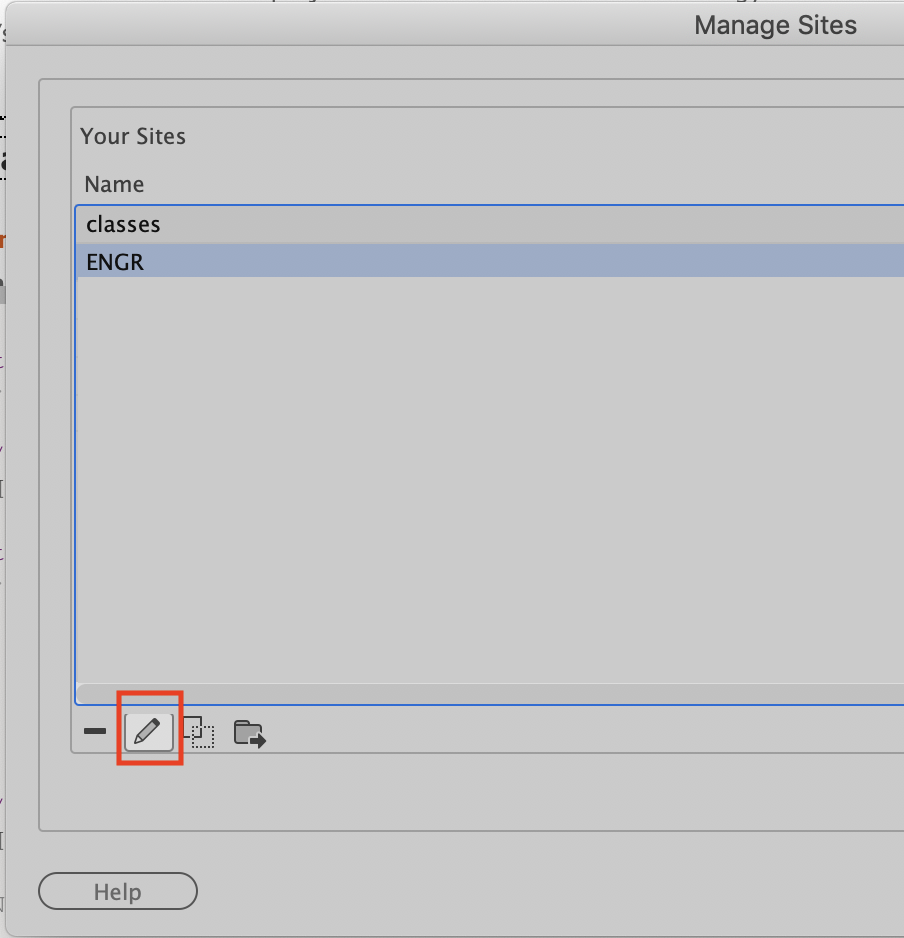
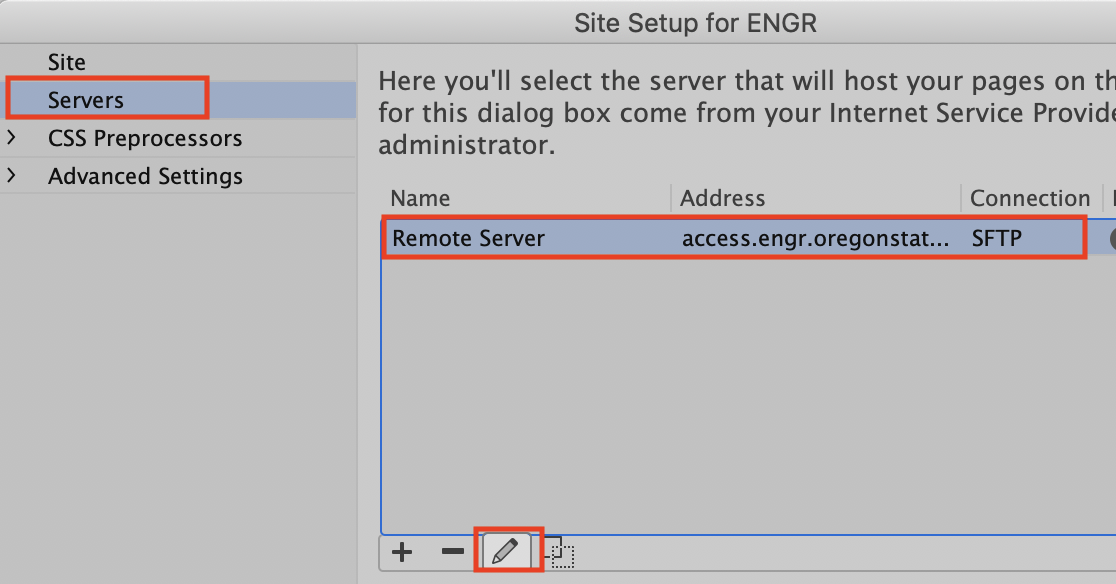
Configure as seen below, navigating to the ssh key file at /Users/[yourUserName]/.ssh/id_rsa
([yourUserName] is YOUR mac login name)
Given the large amounts of different Linux distributions there is no one guide that will work for all. You can use Steps 1-7 of the macOS Guide to generate your keys and publish them to Flip. From that point on you will need to use your FTP client of your choice.
For this you will need:
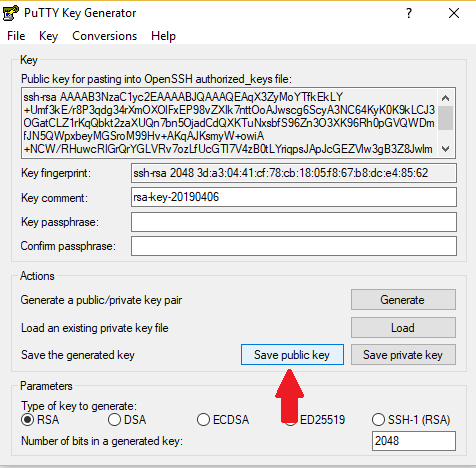
Save it to a location you will be able to easily find it and name it id_rsa.pub
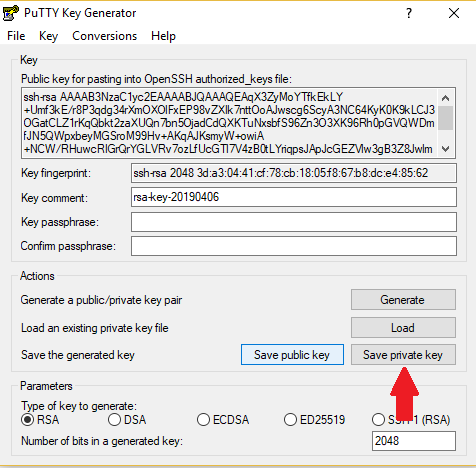
Ignore the warning about the passcode. Save it to the same location as before and name it id_rsa.ppk
access.engr.oregonstate.edu and enter your password when prompted1 and press enter. This will send a request to your Duo Mobile app which you will need to accept.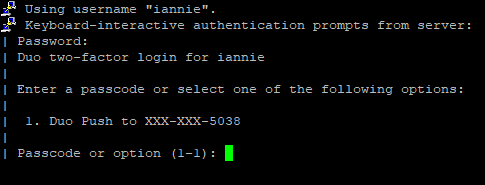
access.engr.oregonstate.edu.ssh does not exist, execute the command mkdir .ssh followed by chmod 700 .ssh~/.ssh/authorized_keys which should be an empty file. If it does not exist, create it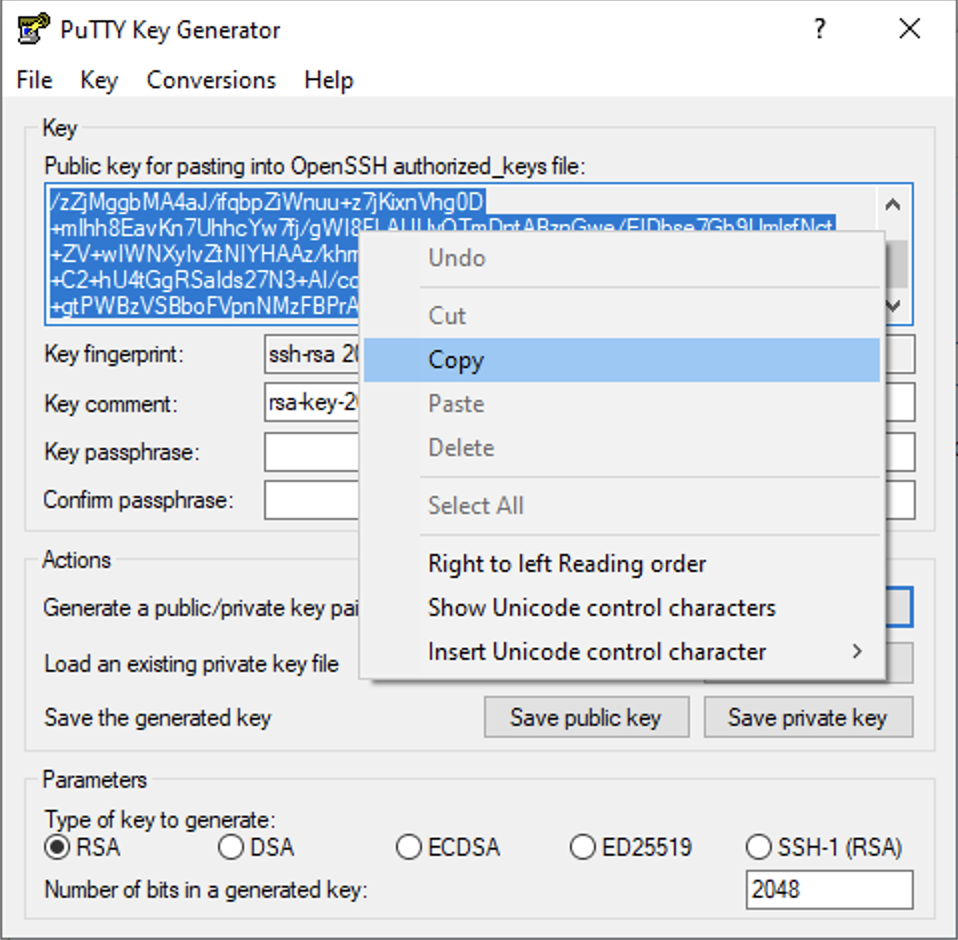
access.engr.oregonstate.edu paste the copied public key and save the changes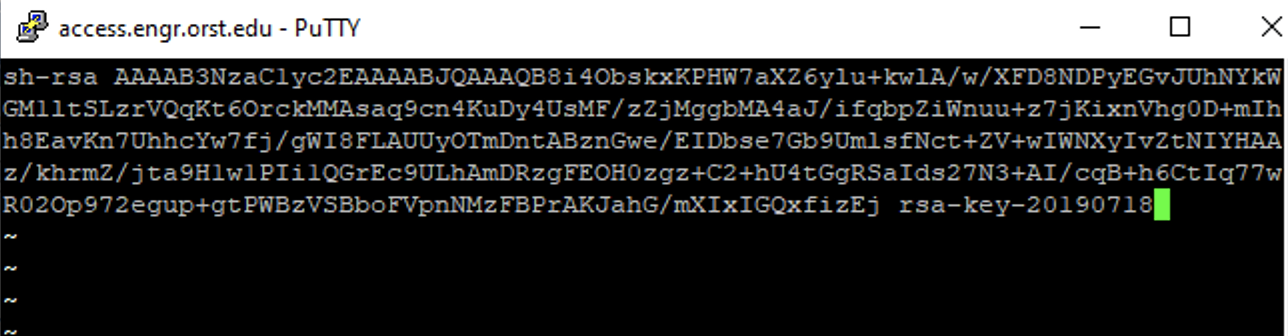
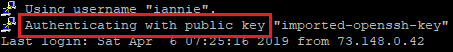
chmod 600 ~/.ssh/authorized_keysyour_username@access.engr.oregonstate.edu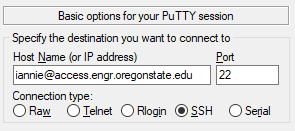
flip and click Save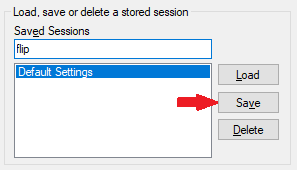
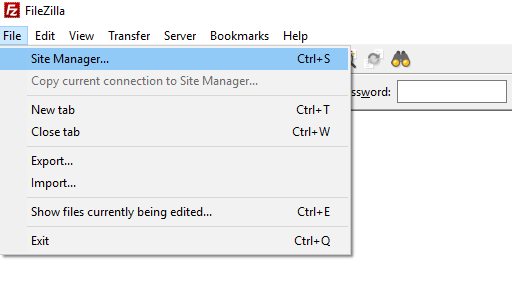
SFTP for the Protocol and enter the Host as access.engr.oregonstate.edu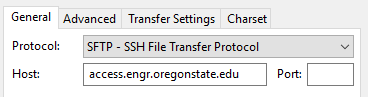
Key file, enter your username for User, and then browse to the location of your `id_rsa.ppk' file.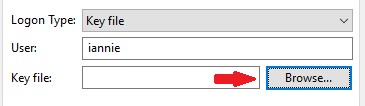
login as:" prompt. 700 (drwx------) and the .ssh/authorized_keys file permission is 600 (-rw-------)